Share this article on:
The NSA and FBI have released a list of the top 15 vulnerabilities routinely exploited by threat actors during 2021.
In a joint advisory partnership with cyber security authorities worldwide, the NSA and FBI urged organisations to promptly patch the security flaws listed and implement patch management systems to reduce their attack surface.
Globally, malicious actors have been observed focusing their attacks on internet-facing systems, including email and virtual private network (VPN) servers, using exploits targeting newly disclosed vulnerabilities.
The advisory stated that the US, Australian, Canadian, New Zealand, and UK cyber security authorities assessed malicious cyber actors that have aggressively targeted newly disclosed critical software vulnerabilities against broad target sets in 2021, which included public and private sector organisations worldwide.
This might be due to malicious actors and security researchers releasing proof of concept (POC) exploits within two weeks since the initial disclosure for most of the top exploited bugs throughout 2021. However, attackers focused some of their attacks on older vulnerabilities patched years before, which shows that some organisations fail to update their systems even when a patch is available.
The list of the top 15 most exploited security flaws is available below:
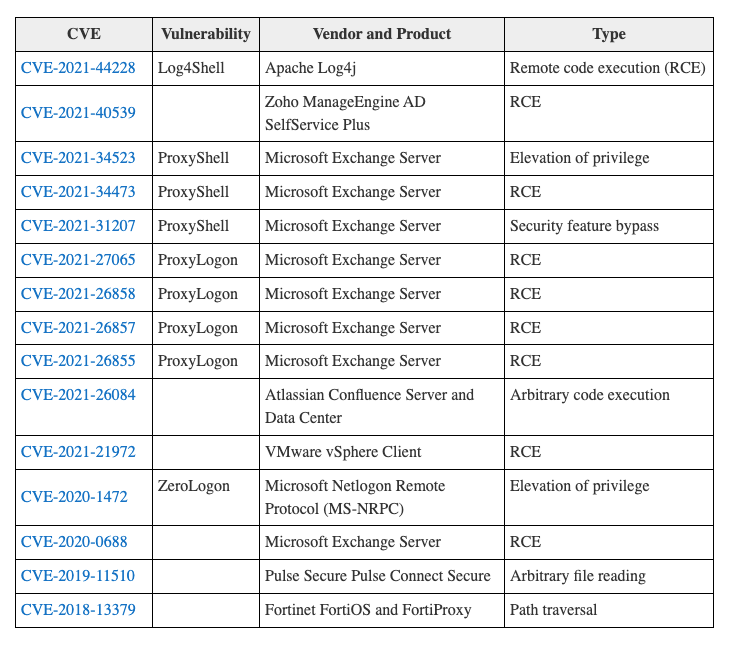
The US, Australian, Canadian, New Zealand, and UK cyber security agencies have also identified and revealed 21 additional security vulnerabilities commonly exploited by bad cyber actors during 2021, including ones impacting Accellion File Transfer Appliance (FTA), Windows Print Spooler, and Pulse Secure Pulse Connect Secure.
The joint advisory includes mitigation measures that should help decrease the risk associated with the topmost abused flaws detailed above.
CISA and the FBI also published a list of the top 10 most exploited security flaws between 2016 and 2019 and a top list of routinely exploited bugs in 2020 in collaboration with the Australian Cyber Security Centre (ACSC) and the United Kingdom’s National Cyber Security Centre (NCSC).
According to CISA director Jen Easterly, the cyber security agency knows that malicious cyber actors go back to what works, which means they target these same critical software vulnerabilities and will continue to do so until companies and organisations address them.
“CISA and our partners are releasing this advisory to highlight the risk that the most commonly exploited vulnerabilities pose to both public and private sector networks.
“We urge all organisations to assess their vulnerability management practices and take action to mitigate risk to the known exploited vulnerabilities,” Easterly said.
[Related: Mailchimp breach led to cyber security ‘negligence’ lawsuit]