Share this article on:
Breaking news and updates daily. Subscribe to our Newsletter
At the end of 2021, Dragos assessed with high confidence that ransomware would continue to disrupt OT operations into 2022. So far, that assessment holds true.
Although we don’t have substantive evidence that the quantity of ransomware incidents has increased year on year, a surge of ransomware initial access campaigns in 2022 shows specific ransomware groups like Conti are more active. Also, the political tension between Russia and western countries may only exacerbate this.
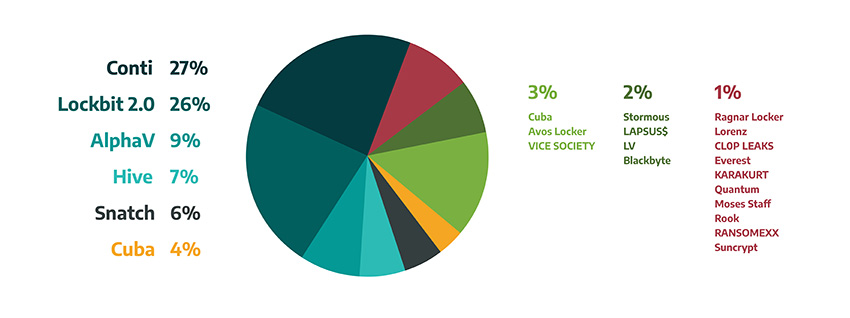
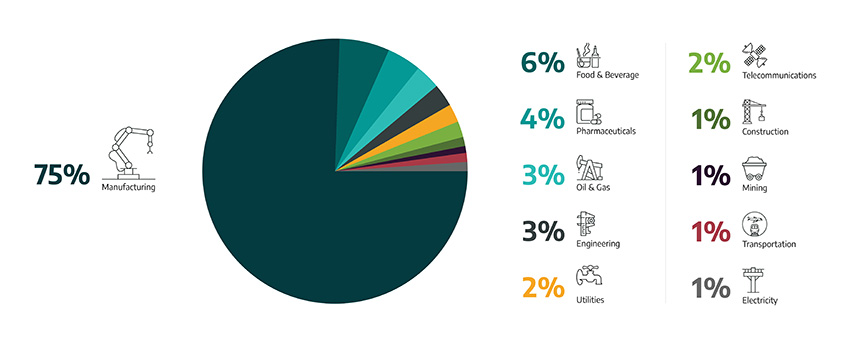
Looking at ransomware targets by region, industry sector (figure 2) and ransomware group (figure 1) in the first quarter of 2022 presents an interesting picture.
The Russian invasion of Ukraine increased the likelihood of impactful cyber activity related to both the industrial infrastructure of the combatants and, arguably, the industrial infrastructure of material supporters of those parties in conflict. The infamous Conti ransomware group declared alignment with the Russian Federation via their Dedicated Leak Site (DLS). It threatened that if any entities directed a cyber-attack or other warfare against Russia, they would use all possible resources to strike back at an enemy's critical infrastructure.
The relatively unsophisticated but effective tactics of the LAPSUS$ theft extortion group showed that large organisations with mature information security regimes are at risk of intrusion and exfiltration. In March, LAPSUS$ posted screenshots of internal software tools tied to several major corporations, including Vodafone, NVIDIA, and Samsung. We assess with low confidence that the LAPSUS$ intrusions may influence ransomware actors to adopt similar techniques that are more resistant to anti-malware defences. Dragos is aware of anti-malware resistant Conti ransomware campaigns in April that ostensibly improve upon their previous hybrid social engineering call centre-based infection campaigns.
We analyse ransomware variants targeting industrial organisations worldwide and track ransomware information via public reports and information uploaded or appearing on dark web resources. By their very nature, these sources under-report targets that pay or otherwise “cooperate” with the criminals and therefore do not match 1:1 with incidents.
Even though the number of ransomware attacks and dark web postings in Q1 2022 is slightly less than Q4 2021, the impacts are larger. Noticeably, attacks disrupted the operations of many large organisations, their suppliers, and subsidiaries. An example is the possible Conti-related ransomware attack in February that targeted Kojima Industries Corp, which supplies Toyota’s plastic parts and electronic components. This incident suspended Toyota plant operations for several days.
In March, a ransomware attack by the Hive group partially impacted some services of Rompetrol, a Romanian oil firm. In February, security researchers discovered a ransomware variant called “HermeticRansom” with destructive capabilities targeting multiple Ukrainian entities. We assess with moderate confidence that adversaries will use it to target other entities.
Ransomware targets by continent show that 81% of all attacks targeted Europe and North America. Globally, 45% of target industrial organisations and infrastructure in North America (36% of that in the U.S.), and Europe at 41%. Australia was only 1%. Ransomware attack targets by sector tracked in Q1 2022 show 75% of all attacks targeted the manufacturing sector, with the remainder spread across food and beverage, pharmaceuticals, oil and natural gas, engineering, utilities and mining.
Analysing the targeted ransomware attacks by group, the data shows Conti made 27% of the total attacks in Q1, followed by Lockbit 2.0 (26%), AlphaV, also known as BlackCat (9%), and Hive (7%). Conti and Lockbit 2.0 maintained nearly a similar percentage of the total ransomware incidents compared to the last quarter of 2021, with most of their victims in the manufacturing sector. Attacks against manufacturing entities often impact other sectors that depend on manufacturers in their operations or supply chain, such as aerospace, food, and beverage, and automotive.
During Q1, we observed trends in the victimology of the ransomware groups. This does not, however, determine the permanent focus of these groups as victimology can change over time. For example, Suncrypt and Quantum have been targeting only Food and Beverage entities, whilst RansomeXX and Rook have been targeting only Pharmaceuticals.
As we continue to analyse and monitor the activities of ransomware families targeting industrial organisations, we publish multiple reports and blogs. In Q2, we assess with high confidence ransomware will continue to disrupt OT operations, whether through the integration of OT kill processes into ransomware strains, flattened networks allowing for ransomware to spread into OT environments, or through precautionary shutdowns of OT environments by operators to prevent ransomware from spreading to OT systems.
To prevent ransomware in your OT environment, learn more here.